Category
IOT & OTA
Two Ways to Update Embedded Devices Over-The-Air
Whether the need is to install the latest security patch, delight customers with new features, or fix bugs - every company must be able to deploy over-the-
|
5 min read
Article | Choosing the right model for maintaining and enhancing your IoT project
In today’s connected embedded device market, driven by the Internet of things (IoT), a large share of devices in development are based on Linux of one form
|
0 min read
Four tools for building embedded Linux systems
Mender's Drew Moseley wrote an article last year that we think is worth highlighting again: Four approaches to build embedded Linux systems, with the advan
|
1 min read
Will the new EU standard protect consumers from IoT products?
The European Telecommunications Standards Institute (ETSI) recently released Technical Specification 103 645, seeking to help protect consumers from IoT de
|
0 min read
What separates leaders from laggards in the Internet of Things
In a recent report, McKinsey shared the findings from a survey of IoT practitioners at 300 businesses with mature IoT programs (those that have expanded be
|
3 min read
Why not homegrown over-the-air update capabilities?
According to Gartner, there will be almost 3 billion new internet-connected devices in 2018. Unfortunately, most of these devices lack basic security featu
|
1 min read
New video introducing Mender and the challenge of remotely updating IoT devices
View our 2 minute video explaining the challenge of updating devices remotely and why Mender should be considered over building your own update mechanism:
|
0 min read
The Need for a World Cybersecurity Organization
"Cyberthreats continue to impose an ever-bigger danger across the fabric of our society. Governments around the world are waking up to this harsh reality a
|
0 min read
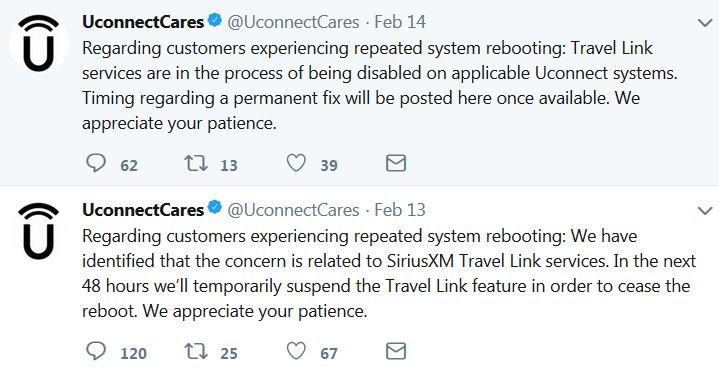
UConnect, more botnets, and poor OTA updating practices
There have been some recent negative press on updating connected devices, including the OTA update that Fiat Chrysler sent out that causes endless reboots
|
2 min read