There have been some recent negative press on updating connected devices, including the OTA update that Fiat Chrysler sent out that causes endless reboots to their UConnect system. Another story that is gaining attention is the infection of tens of thousands of Dasan routers by the Satori malware, which is based on Mirai. Mirai is best known for infecting a large number of connected devices which targeted DNS provider Dyn and brought down large portions of the Internet in October 2016. We wrote an article about the IoT Botnet Wars and some basic security hardening strategies not to be overlooked.
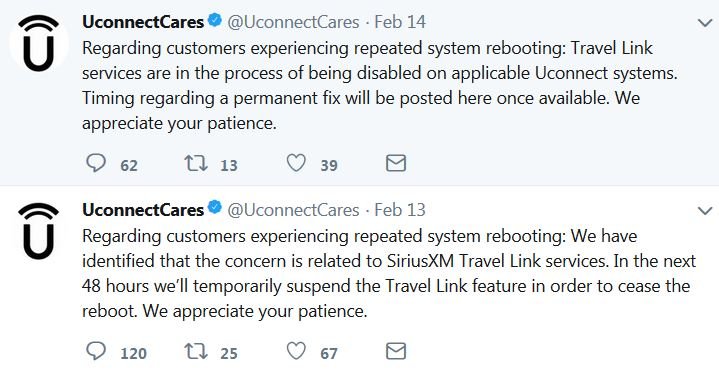
The Fiat Chrysler OTA update is causing certain UConnect systems from 2017 and 2018 to continually reboot the infotainment system with the screen restarting every minute. Unfortunately, it is not just isolated to the SiriusXM radio as the system is also responsible for climate settings, seat heater, and accessing the backup camera. UConnect has given an update that they will disable SiriusXM’s Travel Link services for a temporary fix.
While UConnect has isolated the problem, it is concerning that a major manufacturer did not use commonly accepted best practices for OTA updates. Clearly, there was no rollback. And rather than a phased rollout, the update was deployed all at once - a very risky approach. Another issue was the updates were released on a Friday, not an ideal day if you want to make sure there are resources available to quickly address any issues that may arise. Fiat Chrysler were not able to respond to this issue until Monday.
The Satori botnet that is building primarily off of the routers by Dasan Networks is another troubling story. The router company has maintained radio silence when queried about the exploit. It has been revealed that Satori, which means sudden enlightenment, is exploiting firmware bugs that are left unpatched. Unfortunately, it appears that the malware itself is receiving more updates than the target device.
Recent articles
Ambition is outpacing preparedness: Immature infrastructure projected to fail within five years
The EU CRA regulation: Three key considerations any international company needs to know
CVE-2026-49009 & CVE-2026-33552 - Input sanitization and access control issues in Mender Server
Learn why leading companies choose Mender
Discover how Mender empowers both you and your customers with secure and reliable over-the-air updates for IoT devices. Focus on your product, and benefit from specialized OTA expertise and best practices.



