New Mender experimental AI-enabled feature
Discover Mender's new experimental AI feature that simplifies failure analysis for IoT device updates, saving time and effort for hosted Mender users.
|
4 min read
Categories
Recent posts
View allAmbition is outpacing preparedness: Immature infrastructure projected to fail within five years
Explore the growing complexity of IoT device management and the challenges OEMs face with infrastructure, compliance, and product launches in the latest industry report.
|
5 min read
The EU CRA regulation: Three key considerations any international company needs to know
The EU Cyber Resilience Act (CRA) requires a holistic approach to security compliance for connected products. Discover key considerations from Northern.tech and STMicroelectronics.
|
7 min read
CVE-2026-49009 & CVE-2026-33552 - Input sanitization and access control issues in Mender Server
Two security vulnerabilities recently discovered and fixed in Mender Server.
|
3 min read
CVE-2025-67903 - Signature verification bypass in Mender Client
Security vulnerability enabling signature verification bypass in Mender Client version 5.0.0 to 5.0.3.
|
2 min read
Official release: Mender for Microcontrollers (MCUs), like Zephyr, and the Micro Device Tier
Mender launches support for microcontrollers with the new Micro Device Tier, enabling efficient OTA updates for resource-constrained devices like Zephyr-based MCUs.
|
10 min read
Success with AI in MedTech depends on the software infrastructure beneath it
Explore how robust software infrastructure is essential for the success of AI in MedTech, ensuring compliance, security, and lifecycle sustainability in medical devices.
|
3 min read
Recent posts in IOT & OTA
View allSuccess with AI in MedTech depends on the software infrastructure beneath it
Explore how robust software infrastructure is essential for the success of AI in MedTech, ensuring compliance, security, and lifecycle sustainability in medical devices.
|
3 min read
Succeeding in the IoT product landscape: How OEMs align AI, software, and time-to-Market
Discover how OEMs can effectively align AI and software to enhance their IoT products, tackle time-to-market challenges, and ensure long-term success.
|
4 min read
What’s new in Mender: New Update Modules for container updates
Discover Mender's new Update Modules for OTA container updates, enhancing deployment efficiency and network reliability for seamless software updates.
|
3 min read
Beyond traditional connectivity: managing smart products and machines in air-gapped and offline environments
Explore how to manage smart devices in air-gapped and offline environments with secure, authenticated software updates, ensuring compliance and operational efficiency.
|
7 min read
Key considerations: How to build compliant software update practices for medical devices
Learn how to implement compliant software update practices for medical devices while navigating FDA and EU MDR regulations, ensuring safety and cybersecurity.
|
7 min read
Mender Client 6.0 released
Discover the new features in Mender Client 6.0, including official Docker Compose support and enhanced network robustness for reliable IoT device updates.
|
2 min read
Recent posts in customer story
View allCutting costs by 80%: Sustainable energy innovator leverages OTA updates
Discover how a leading sustainable energy innovator reduced production costs by over 80% while maintaining secure, scalable OTA updates across Linux and Zephyr platforms.
|
4 min read
Sustainable devices, smart innovation: How OTA updates can contribute to cutting costs and carbon
Discover how OTA updates help companies like Kuva Systems and Beegy reduce emissions, cut costs, and build smarter, more sustainable IoT systems.
|
5 min read
Enhancing maritime security and connectivity: The critical role of OTA updates in fleet management
Explore the critical role of OTA updates in maritime fleet management, ensuring enhanced security, performance, and continuous connectivity across vessels.
|
7 min read
Enhancing sustainability in oil & gas: Tackling methane emissions with cutting edge solutions
Discover how Kuva Systems overcame challenges in managing methane emission monitoring cameras in the oil & gas industry with advanced OTA updates and remote troubleshooting.
|
3 min read
How over-the-air (OTA) updates help emergency response teams
Discover how over-the-air (OTA) updates revolutionize emergency response teams, ensuring secure and seamless device maintenance and functionality in critical situations.
|
4 min read
Enhancing mobility and safety for citizens: a smarter power wheelchair can increase the user's independence and real-world technology inclusion
Users of conventional power wheelchairs can face some significant challenges, including avoiding collisions, drop-offs, and tips. Kevin Lannen, Senior Embe
|
3 min read
Recent posts in product news
View allOfficial release: Mender for Microcontrollers (MCUs), like Zephyr, and the Micro Device Tier
Mender launches support for microcontrollers with the new Micro Device Tier, enabling efficient OTA updates for resource-constrained devices like Zephyr-based MCUs.
|
10 min read
New Mender experimental AI-enabled feature
Discover Mender's new experimental AI feature that simplifies failure analysis for IoT device updates, saving time and effort for hosted Mender users.
|
4 min read
What’s new in Mender: Enhanced delta updates and user experience
Discover Mender's latest enhancements in delta updates and user experience, including server-side delta generation and user-friendly subscription management, in our newest product release.
|
3 min read
New Mender packaging and distribution channels
Simplify installing and updating Mender with new apt repositories, improving security, dependency handling, and version control.
|
3 min read
Mender Client 5.01 and 5.0.2 releases: Enhanced reliability and stability for production IoT deployments
Learn more about the latest bug fixes and improvements to Mender with the release of Mender Client 5.0.2.
|
3 min read
Service Provider tenant: SSO enhancements
Learn more about the Single Sign-on (SSO) enhancements in the new Service Provider tenant in Mender Server 4.0.
|
6 min read
Recent posts in engineering
View allOver-the-air update strategies for Raspberry Pi-based embedded systems
Discover effective OTA update strategies for Raspberry Pi-based embedded systems using Mender, focusing on system-level and application-level updates for reliability and efficiency.
|
4 min read
Over-the-Air Updates on Raspberry Pi
Learn how to deploy over-the-air updates for Raspberry Pi devices with Mender, exploring system and application update methods for IoT projects.
|
4 min read
How to leverage over-the-air (OTA) updates for NVIDIA Jetson Platform Services
To enable software installation, updates, management, and support across the Jetson device fleet and at scale – Mender, in collaboration with NVIDIA, published three critical use cases for NVIDIA developers.
|
2 min read
First alpha version of Mender C++ client released
We have reached the first milestone of the Mender client rewrite to C++: the first alpha version is now available! There are still a lot of features missin
|
4 min read
Mender OTA on the ESP32, Part 2
In the second of a two-part blog series, Josef Holzmayr, Head of Developer Relations, examines how community member Joël Guittet developed an integration f
|
6 min read
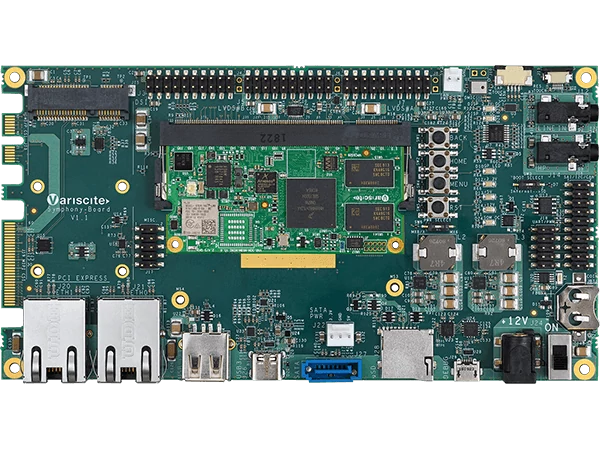
Over-the-air (OTA) integration: Variscite VAR-SOM-MX8M-MINI and Yocto Kirkstone
The VAR-SOM-MX8M-MINI offers the latest video and audio experience, combining state-of-the-art media-specific features with high-performance processing opt
|
3 min read
Recent posts in cybersecurity
View allDriving secure innovation: ISO/SAE 21434 & UNECE compliance
ISO/SAE 21434 and UNECE R155/R156 standards reshape cybersecurity in software-defined vehicles. Compliance with these frameworks is essential for protecting consumers, ensuring vehicle safety, and driving innovation in the automotive industry.
|
7 min read
Understanding the EU Cyber Resilience Act (CRA): Why it matters and how to comply
The EU Cyber Resilience Act (CRA) was enacted in October 2024 and has impacted products with digital elements on the European market. Learn why CRA compliance is essential for manufacturers, the penalties for noncompliance, and how to meet the Act's cybersecurity standards.
|
6 min read
Recent posts in CRA
View allThe EU CRA regulation: Three key considerations any international company needs to know
The EU Cyber Resilience Act (CRA) requires a holistic approach to security compliance for connected products. Discover key considerations from Northern.tech and STMicroelectronics.
|
7 min read
Why cloud IoT solutions alone are not EU CRA compliant
Cloud IoT solutions often fall short in achieving compliance with the EU CRA. Learn more about the extensive requirements, and proper management solutions.
|
4 min read
Does EU CRA compliance require advanced OTA update capabilities?
Learn about the requirements of the EU CRA. Outlining the importance of robust OTA update capabilities as a cornerstone of CRA compliance.
|
7 min read
The power of over-the-air (OTA) updates in patch management
Learn about the power of over-the-air (OTA) updates in patch management. Outlining the importance of robust capabilities in enhancing CRA compliance.
|
4 min read
The European Union Cyber Resilience Act (CRA): Why remediation requires over-the-air (OTA) updates
Discover how over-the-air (OTA) updates are essential for meeting the EU Cyber Resilience Act (CRA) requirements.
|
5 min read
Challenges in complying with the EU Cyber Resilience Act (CRA)
Discover how manufacturers can achieve Cyber Resilience Act (CRA) compliance by tackling secure updates, SBOM management, and vulnerability tracking with robust OTA solutions.
|
8 min read
Recent posts in events
View allWhy OTA updates are now mission critical for future-proofed device lifecycle management
Discover why Over-The-Air (OTA) updates are essential for future-proofing IoT device lifecycle management, ensuring security, compliance, and continuous improvement in an evolving technological landscape.
|
6 min read
IoT Slam 2025: The impact of AI
The recent IoT Slam 2025 conference outlined cutting-edge trends and technologies covering the entire spectrum of IoT across industries.
|
4 min read
The role of open source software in embedded systems
Discover the role of open source software in embedded systems with insights from Yocto and inovex on transparency, security, and the evolving OSS landscape.
|
7 min read
The reach of AI: Digital, edge, physical, and beyond
The recent NVIDIA GTC 2025 conference outlined AI developments. Learn more about simulations, data generation, and the importance of OTA updates in growing AI capabilities.
|
6 min read
Robust OTA updates with A/B Partitions for Linux devices
Discover insights from Embedded World 2025 on A/B partitions for secure OTA updates, reducing fragmentation, and streamlining embedded system firmware updates.
|
7 min read
Key takeaways from embedded world North America 2024
The Mender team attended the first embedded world in North America to connect with industry leaders and discuss insights on IoT compliance, the CRA, RTOS vs. Linux for IoT, and the importance of secure OTA update orchestration.
|
5 min read
Recent posts in CVE
View allCVE-2026-49009 & CVE-2026-33552 - Input sanitization and access control issues in Mender Server
Two security vulnerabilities recently discovered and fixed in Mender Server.
|
3 min read
CVE-2025-67903 - Signature verification bypass in Mender Client
Security vulnerability enabling signature verification bypass in Mender Client version 5.0.0 to 5.0.3.
|
2 min read
CVE-2025-49603 - Improper access control of device groups in Mender Server
An ethical hacker on our HackerOne private bug bounty program recently discovered and disclosed access control issues with device groups in Mender Server.
|
3 min read
CVE-2024-55959 - Insecure permissions on private key file generated by the Mender Client
A customer recently notified us of a security issue in Mender. On some versions, mender-auth generates private key files with non-strict file permissions.
|
3 min read
CVE-2024-46947 & CVE-2024-47190 - SSRF issues in Mender Enterprise Server
Recently discovered security vulnerabilities in Mender Server have been fixed.
|
3 min read
CVE-2024-46948 - Missing filtering based on RBAC device groups
A customer recently notified us of a security issue in Mender. For users of RBAC and device groups, one specific API did not filter devices correctly.
|
1 min read
Subscribe to our newsletter
Get the latest posts delivered to your email.
By signing up, you agree to your email address being stored and used to receive newsletters about Mender. We use tracking in our newsletter emails to improve our marketing content.
Customer spotlight
Technical articles
Learn more about Mender
Explore our Resource Center to discover more about how Mender empowers both you and your customers with secure and reliable over-the-air updates for IoT devices.
























.jpg?length=720&name=shutterstock_1875500836%20(1).jpg)




.jpg?length=720&name=IMG_5253%20(1).jpg)